Boundless Intrusion – it’s much bigger than Prism
 The recent flurry caused by Edward Snowden’s revelations on Prism is welcome – this area needed a more light casting on it, and certainly more oversight. But Prism is neither the biggest program or a new thing – this has been going on for a decade or more…..
The recent flurry caused by Edward Snowden’s revelations on Prism is welcome – this area needed a more light casting on it, and certainly more oversight. But Prism is neither the biggest program or a new thing – this has been going on for a decade or more…..
A couple of things strike me about the current arm-waving about Prism. One is the indignation of some Americans that they are being spied on. No American I ever met had any issue about eavesdropping on foreigners -including their allies. But they get red in the face if they think it’s happening to them, making the whole thing quite enjoyable if you’re one of the spied upon. The second is the focus on Prism in the debate – that is the ability to tap into the servers of the main internet players. Prism is much the less interesting of the revelations though. Far more interesting are Fairview, Blarney, Boundless Informant, and Tempora.
 Around 8 years ago I remember a discussion with a well placed liaison guy with the NSA in which he said matter of factly that the US then could intercept all the communications of anyone in the the world. This included phone calls, emails, texts, and in fact any communications traffic. Of course he said this only applied to foreigners, and I thought right, yep. sure. The technical issue then was not the interception, it was interpretation and storage. Because at the time storage costs were higher and processing speeds lower, they could not store it all and had to have the fastest possible systems to process the data in-line, and pull out only the interesting stuff for later analysis. The issue was not capability – it was capacity. All that has happened since is that the capacity has increased by leaps and bounds. Firstly storage costs have dived. Secondly, low-cost, high-speed GPUs (the same myriad of little processors that power graphics processor cards in PCs) have transformed the analysis process. Formerly they were doing this with massive high-end general-purpose systems. Now they do this with millions of little custom processing units at low cost and incredible speed. By the way, it’s these little units that have also transformed the ability of criminal hackers to crack your passwords.
Around 8 years ago I remember a discussion with a well placed liaison guy with the NSA in which he said matter of factly that the US then could intercept all the communications of anyone in the the world. This included phone calls, emails, texts, and in fact any communications traffic. Of course he said this only applied to foreigners, and I thought right, yep. sure. The technical issue then was not the interception, it was interpretation and storage. Because at the time storage costs were higher and processing speeds lower, they could not store it all and had to have the fastest possible systems to process the data in-line, and pull out only the interesting stuff for later analysis. The issue was not capability – it was capacity. All that has happened since is that the capacity has increased by leaps and bounds. Firstly storage costs have dived. Secondly, low-cost, high-speed GPUs (the same myriad of little processors that power graphics processor cards in PCs) have transformed the analysis process. Formerly they were doing this with massive high-end general-purpose systems. Now they do this with millions of little custom processing units at low cost and incredible speed. By the way, it’s these little units that have also transformed the ability of criminal hackers to crack your passwords.
 In the slide on the left, the upstream and downstream data collection routes are outlined. It’s the upstream, inline ones we’ll look at first. These are Fairview and Blarney, to which can now be added the UK GCHQ’s Tempora, and an overarching meta-program, Boundless Informant.
In the slide on the left, the upstream and downstream data collection routes are outlined. It’s the upstream, inline ones we’ll look at first. These are Fairview and Blarney, to which can now be added the UK GCHQ’s Tempora, and an overarching meta-program, Boundless Informant.
How does this process work? What has happened for probably the last 11-12 years is that NSA, GCHQ and others sit on top of the key nodes in the worldwide internet, and tap directly into the flow. The key players they co-opt are the tier 1 internet backbone carriers like CenturyLink, Cable & Wireless Worldwide, UUNet, Sprint, AT&T Corporation, and Genuity (not the likes of Google and Microsoft). They probably also tap right into the Internet exchange points that ISPs use to minimise traffic over the international backbones. It’s very interesting to me, but barely picked up by the press, that even for the Prism programme “access is 100% dependent on ISP provisioning”. If you were getting all your information directly from the Googles of the world, why would you need the ISPs?
So anyway, as detailed in the Guardians GCHQ revelations of today, in-line processing filters out the “high-volume, low-value traffic, such as peer-to-peer downloads, which reduces the volume by about 30%.” They can now store the rest for 3 days – an amazing achievement. They can store all the metadata for 30 days. All this generates such a colossal volume of information, they need a high-end system just to be able to navigate it. That system is called Boundless Informant, and it provides the ability to more closely locate the needle in the haystack the NSA may be looking for.
By the way, you are probably aware that if you work for any large company, they can track all your emails and communications. Do you think they get that from Google? Nope, they just intercept all your internet traffic, in a small-scale version of the NSA’s programmes.
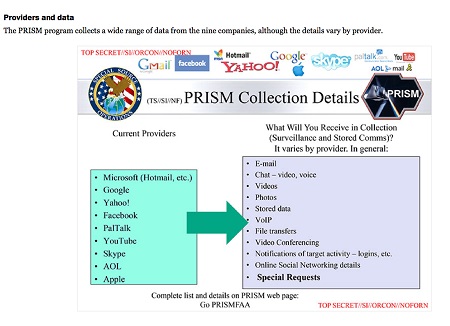 So what is Prism? Well the in-line analysis, captures everything from everybody, including everything you send to and from Gmail, Facebook, Microsoft, Apple etc, and all phone conversations. However, what it doesn’t do is to put it into any kind of logical order. To do that would require the NSA to recreate Google’s infrastructure. Why do that when Google (to use them as an example) has spent billions creating their own? So the simplest thing is once you know your target, to tap into Google’s servers to get all the data neatly ordered. That’s what Prism does. The fact that Google and the others respond to requests of this kind was known long before Edward Snowden’s revelations. The thing that seems to have alarmed people is that this might in some way be automated, via a ‘back door’. Automated or not, it’s not Prism that’s the threat to liberty in my view, its the in-line eavesdropping. Without it, the intelligence agencies would have to rely on old-fashioned intelligence to get sufficient information to justify a Prism request. But with every single piece of communication used by any individual, it’s trivially easy to find some piece of possibly innocuous but suspicious looking data that would support getting full access to Google’s servers for that individual.
So what is Prism? Well the in-line analysis, captures everything from everybody, including everything you send to and from Gmail, Facebook, Microsoft, Apple etc, and all phone conversations. However, what it doesn’t do is to put it into any kind of logical order. To do that would require the NSA to recreate Google’s infrastructure. Why do that when Google (to use them as an example) has spent billions creating their own? So the simplest thing is once you know your target, to tap into Google’s servers to get all the data neatly ordered. That’s what Prism does. The fact that Google and the others respond to requests of this kind was known long before Edward Snowden’s revelations. The thing that seems to have alarmed people is that this might in some way be automated, via a ‘back door’. Automated or not, it’s not Prism that’s the threat to liberty in my view, its the in-line eavesdropping. Without it, the intelligence agencies would have to rely on old-fashioned intelligence to get sufficient information to justify a Prism request. But with every single piece of communication used by any individual, it’s trivially easy to find some piece of possibly innocuous but suspicious looking data that would support getting full access to Google’s servers for that individual.
There is one more – intangible – question about this – what does it mean for you and me? Isn’t this snooping justified given that people in the UK and elsewhere are probably planning to blow us up as we speak? I would support this argument except that it is trivially easy for people who are aware of this capability to never use wording that betrays any felonious intent. We all know already that we should not use words like b*mb in our emails. I guess this may also be known to suspected terrorists. I could be wrong, but I suspect that even if the US agencies do not place all potential terrorist suspects under direct human surveillance, they certainly monitor their communications traffic – it’s so easy and cheap to do. And that turned up nothing in the case of the Boston Marathon bombers. So the main use of the snooping is probably in more trivial or non-terrorist areas. Like if you are proposing to go on an anti-government demonstration, or interrupt Vodafone’s AGM. Or indeed if you are an active member of Greenpeace and don’t like MacDonalds (if you think the authorities are happy to co-write incendiary literature and impregnate potential targets – do you think they would balk at intercepting emails?)
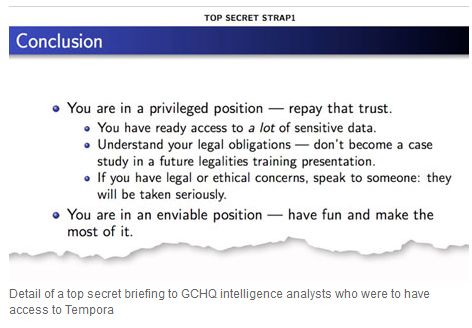
In the UK the discontent leading to terrosism is bred and can be observed in the streets and the Madrassas. That’s where the UK should be spending it’s time and money. But the technology is way more fun, particularly if you can spy on your friends, as we appeared to do to the Turks in 2009 and presumably ever since. For proof of the ‘fun’ aspect by the way, look at the last line in the GCHQ slide below (from the Guardian again) – read it and weep.