If you have a Yahoo or Flickr account, read this!
 Like many people, I have a Yahoo account (for news updates and Flickr). Now it appears that 500 million Yahoo accounts, including probably mine, have been accessed, by a ‘foreign state actor’. And 200 million of them are now for sale on the dark web. I regarded Yahoo and other non-financial and non-critical sites as a low risk, and used the same password on many of them. I just did an analysis of how many places I had used the same password. It turns out to have been 60! Quite a lot. Some of those have information like phone numbers and my address. So I have just been through them all, giving them strong individual passwords. I suggest you do the same. But just how risky is this breach?
Like many people, I have a Yahoo account (for news updates and Flickr). Now it appears that 500 million Yahoo accounts, including probably mine, have been accessed, by a ‘foreign state actor’. And 200 million of them are now for sale on the dark web. I regarded Yahoo and other non-financial and non-critical sites as a low risk, and used the same password on many of them. I just did an analysis of how many places I had used the same password. It turns out to have been 60! Quite a lot. Some of those have information like phone numbers and my address. So I have just been through them all, giving them strong individual passwords. I suggest you do the same. But just how risky is this breach?
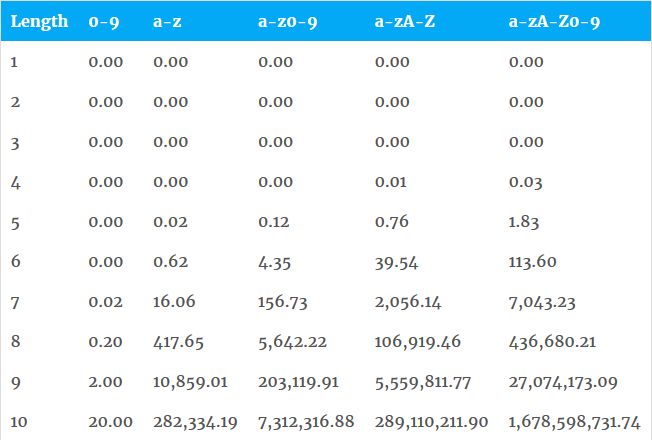
The stolen Yahoo passwords are supposed to have been encrypted. The most widely used ‘strong’ password encryption standard is ‘salted MD5 hashing’. Technology has moved so fast now that anyone with a $400 Nvidia PC graphics card (GPU) can use ‘brute force’ to decode these passwords. The table below shows the real impact on the time it takes to crack a password of the number of characters (first column of the table) and the complexity of the password (first row of the table, ranging from numbers only on the left, to numbers plus lower and upper case letters on the right). So how long does it take to decode a strong (salted MD5 hash) password in seconds? Not long it turns out. A 6 character password using a mix of lower case letters and numbers which you might have thought to be quite secure, takes just 4 seconds to crack. That cracked password is worth real cash to a hacker, so for 4 seconds on some cheap PC hardware, they are going to invest some time and money. If you had a Yahoo or Flickr account you are highly vulnerable.
The moral is, use AT LEAST a minimum of 8 characters with a mix of lower case, and upper case characters, symbols, and numbers (that combination would take 5 days to crack with today’s GPU cards). Yahoo say that ‘the majority’ of their passwords were encrypted with the stronger ‘bcrypt’ method. But it’s only a matter of time before the speed of the GPUs and the smarts of the hackers (this table is produced by a hacker) will catch up with that also. And in the recent breaches of Dropbox, Linkedin and Adobe, the passwords all had very poor (SH1) or NO encryption. So be careful. Make sure all your passwords are long, strong, and unique!